Reward your researchers fairly – try our bug bounty calculator today!
Global crowdsourced security provider trusted by the world's leading organizations
Our clients include
Why Intigriti?
Security that works the way you do
Pair always-on, real-world bug bounty coverage with on-demand PTaaS for security deep dives. Get ultimate testing flexibility powered by the crowd, unified on a single platform.
Elite global talent
Tap into the diverse expertise of 150K+ vetted security researchers (also known as ethical hackers) to instantly extend your team. They find real‑world threats scanners and pentests miss - closing your skills gap with specialisms in mobile, web, AI, APIs, IoT, and more.
Agility meets security
Threats evolve. Your security should too. Easily flex your budget: continuous testing with bug bounty and managed VDPs, plus targeted PTaaS when you need it. Adapt your security strategy to your evolving attack surface.
Pay for impact
Pay only for confirmed vulnerabilities. Our expert triage team vets every submission from our ethical hackers - cutting out false positives and duplicates so your team can focus on fixing, not sifting through submissions.
Active programs
400+
Hundreds of companies trust Intigriti to protect their digital assets through continuous security testing powered by ethical hackers worldwide.
Researchers
150K+
A global community of 150,000+ verified security researchers helps uncover vulnerabilities before malicious actors can exploit them.
Bounties paid
€60M+
Intigriti has rewarded over €60 million in bug bounties, recognizing the vital contributions of researchers who make the internet safer every day.
Product types
Whether you need bug bounty alone or a blend of continuous and focused testing, we’ll shape the right solution for your security goals.
Bug bounty
Find vulnerabilities before they can be exploited with our global network of ethical hackers testing your assets 24/7. Stay ahead of threats with tailored programs built for your security needs.
PTaaS
Pentest as a Service
Get precise, time‑boxed testing to meet compliance and bolster assurance - with expert-led execution and pay‑for‑value efficiency.
Managed VDP
Empower researchers to safely report vulnerabilities. Intigriti manages triage and validation so your team focuses only on genuine threats.
Live hacking events
Create buzz while boosting security. Engage the crowd to find critical bugs in a dynamic, competitive environment.
Are you a security researcher?
We are the fastest-growing community of ethical hackers and security researchers. Help leading companies protect their assets and earn bug bounty rewards while doing it.
Trusted by industry leaders
Discover why Grafana chose Intigriti for their bug bounty needs
Explore more customer stories below to learn how other organizations like Intel, Microsoft, and Personio leverage bug bounty and the crowd to strengthen their security posture.
Our unfair advantages
Industry-leading triage speed and accuracy. Get validated vulnerability findings fast – it's a top reason customers choose Intigriti.
Ultimate flexibility. Scale programs to your security needs – one subscription, no forced upgrades or hidden costs.
True EU data sovereignty. GDPR-compliant with data hosted exlusively in Europe, protected from foreign data seizure.
Military-grade encryption. The only bug bounty platform with application-layer encryption.
Take a platform tour
Ready to experience Intigriti's platform?
Take a live demo and explore the dynamic capabilities firsthand. Empower your security and development workflows with our multi-solution SaaS platform, that can merge into your existing processes.
What our customers have to say
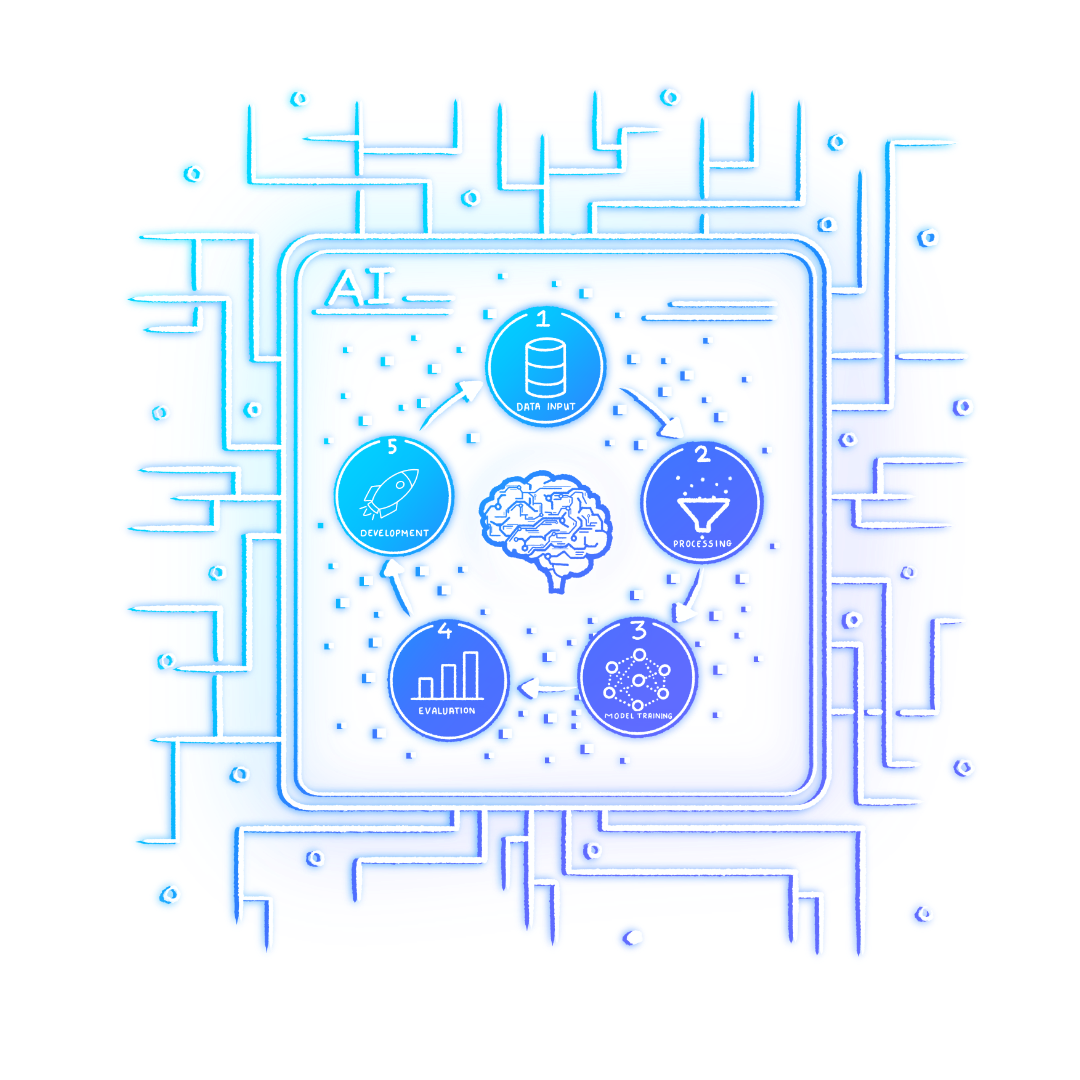
Signal Through the Slop: The 2026 Security Forecast
6 key insights from Intigriti on navigating AI hallucination, supply chain risk, and the new vulnerability landscape.
Drawing on Intigriti observations and data gathered throughout 2025, this report examines threats seen in practice and the trends expected to grow, evolve, and define the cybersecurity landscape throughout 2026.
The latest news
We are delighted to share that Intigriti has won Best Security Company (under 250 employees), at this year’s SC Awards Europe. For over 25 years, the SC Awards Europe have defined what excellence looks like in cybersecurity, recognizing the organizations, technologies, and leaders shaping the futu
Based in the Netherlands, Stefan Goossens, otherwise known as G0053, is both an independent security researcher and a partner for a marketing and web development company. As someone who loves nothing more than building and breaking web applications, Stefan is perfectly placed at the intersection of
Security teams running Bug Bounty programs often require similar insights and reporting to prove the value and ROSI for security initiatives, and often ask questions such as: What changed? Where are we spending? Are we improving? What needs attention right now? Until now, answering thos
Frequently asked questions
Crowdsourced security is when a company invites the crowd, this being a large group of security researchers and ethical hackers, to help search for vulnerabilities in their digital systems, applications and environments, rather than relying on traditional forms of security testing.
Read this eBook on an introduction to crowdsourced security.
Used together, VDP, Bug Bounty, and PTaaS provide defense in depth: VDP for broad visibility, Bug Bounty for targeted depth, and PTaaS for structured assurance. A layered approach gives you wider coverage, deeper testing, and stronger control, protecting your business against both common and advanced threats.
Learn how to combine these approaches in this blog.
Security Maturity is a term used to define an organization’s ability to detect, manage, and mitigate security vulnerabilities and risks. It reflects how well the organization applies programs, processes, and controls to protect its assets and data. Generally, a higher security maturity posture indicates a stronger capability to identify and respond to cyber threats.
Bug bounty, VDP, and PTaaS support companies in their maturity journey by engaging in proactive, rather than reactive, security.
Fast and accurate triage, trusted by both researchers and customers, multi-layered encryption, cost efficiency, robust focus on GDPR and EU legal compliance, trusted ID verification, and a clear code of conduct.
Read about Intigriti’s impact here.